Disclaimer: This article is for educational and informational purposes only and is not investment advice. The views expressed are those of the author and do not constitute recommendations to buy, sell, or hold any securities or make any investment decisions. Readers should conduct their own research and consult with qualified financial advisors before making investment decisions.
The Clock Is Ticking Faster Than We Thought
In February 2026, something remarkable happened in Hefei, China. Origin Quantum Computing Technology released Origin Pilot—the world’s first open-source quantum operating system available for public download. A week later, researchers at Iceberg Quantum published a paper demonstrating that breaking RSA-2048 encryption might require fewer than 100,000 qubits, not the million-plus previously estimated. Then, in early March, the Advanced Quantum Technologies Institute announced the JVG Algorithm, claiming it could crack RSA with fewer than 5,000 qubits.
If you’re in finance, these aren’t just academic milestones. They’re alarm bells.
For years, the quantum threat to encryption has been treated as a distant, theoretical concern—something to worry about in 2040 or 2050. But the convergence of breakthroughs in February and March 2026 tells a different story. “Q-Day”—the moment when quantum computers can break current encryption—is approaching faster than most financial institutions are prepared for. And the most insidious threat isn’t even about the future. It’s about the data being collected right now.
What’s Happening: The Quantum Leap Forward
To understand why 2026 is a watershed year, you need to grasp how rapidly the quantum computing landscape is evolving. Just seven years ago, in 2019, Google Quantum AI estimated that breaking RSA encryption would require 20 million qubits. By 2025, that number had dropped to less than a million. Now, in February 2026, Iceberg Quantum’s Pinnacle Architecture—leveraging advanced Quantum Low-Density Parity-Check (QLDPC) codes—has reduced the requirement to approximately 98,000 superconducting qubits to break RSA-2048 in about a month, or 471,000 qubits to do it in a day.
Think about that trajectory. We’ve gone from 20 million to under 100,000 in seven years. That’s not linear progress—it’s exponential compression of the attack surface.
The Breakthroughs Reshaping the Timeline
Origin Pilot: Democratizing Quantum Development
China’s release of Origin Pilot is significant not because it immediately threatens encryption, but because it lowers the barrier to entry for quantum research globally. The open-source operating system supports multiple hardware platforms—superconducting qubits, trapped ions, and neutral atoms—and powers Origin Wukong, China’s third-generation superconducting quantum computer with 198 physical qubits. The Wukong cloud platform has already attracted over 30 million visits from 120+ countries, executing more than 339,000 quantum computing jobs.
This democratization accelerates innovation. When quantum development tools are freely available, progress compounds faster. It’s the same dynamic we saw with open-source AI frameworks like TensorFlow and PyTorch—except this time, the stakes involve the cryptographic foundation of global finance.
QLDPC Codes: The Efficiency Revolution
The real game-changer is the advancement in quantum error correction through QLDPC codes. Traditional surface codes require about 511 physical qubits to create a single logical qubit at a given error-correction distance. QLDPC codes, by contrast, can encode 14 logical qubits in approximately 860 physical qubits at the same distance. This dramatic efficiency gain—roughly 8x improvement—is what enabled Iceberg Quantum’s Pinnacle Architecture to slash the qubit requirements for breaking RSA.
IBM transitioned to QLDPC codes in 2024, and industry experts predict other major players will follow suit in 2026. The shift isn’t just about raw qubit counts anymore; it’s about building complete, fault-tolerant quantum computers (FTQCs) that can reliably perform computations despite noise. The new metric to watch is “error-free Quantum Operations” (QuOps)—a measure of what quantum systems can actually achieve, not just theoretical advantage.
Quantinuum’s Hybrid Milestone
In March 2026, Quantinuum demonstrated a breakthrough in hybrid quantum-HPC computing, successfully executing a full scientific workflow across its Reimei quantum computer and Japan’s Fugaku supercomputer. This isn’t just a technical achievement—it’s a proof of concept that quantum and classical systems can work together seamlessly. The company’s Helios quantum computer, scheduled for deployment in Singapore in 2026, features industry-leading fidelity and a fully connected qubit architecture. With backing from JPMorgan, NVIDIA, Mitsui, and Amgen, and a confidential IPO filing targeting a $10 billion valuation, Quantinuum is positioning itself at the intersection of quantum computing and enterprise applications.
For financial institutions, this matters because it shows quantum computing is transitioning from lab curiosity to production-ready infrastructure.

Why It Matters: The “Harvest Now, Decrypt Later” Threat
Here’s the part that should keep every CISO, CTO, and CFO awake at night: the quantum threat isn’t just about the future. It’s about today.
The “Harvest Now, Decrypt Later” (HNDL) attack vector is elegantly simple and devastatingly effective. Adversaries—whether nation-states, organized crime syndicates, or sophisticated hacking groups—are collecting encrypted data right now. They can’t decrypt it with current technology, but they don’t need to. They’re storing it, waiting for the day when quantum computers become powerful enough to crack the encryption retroactively.
Think about the data your institution is encrypting today:
- M&A negotiations and strategic plans that could be valuable for years
- Proprietary trading algorithms that represent billions in competitive advantage
- Customer financial records with decades of retention requirements
- Regulatory filings and compliance documentation with long-term legal implications
- Intellectual property and research data that underpins future products
If Q-Day arrives in 2030—a timeline that now seems plausible given recent breakthroughs—then any data encrypted today with RSA-2048 could be vulnerable within four years. For data that needs protection for 20 or 30 years, the clock has already run out.
At Savanti Investments, we’ve been thinking about this problem through the lens of quantitative trading. Our QuantAI™ platform processes vast amounts of market data and executes strategies based on proprietary algorithms. If those algorithms were compromised—if a competitor could decrypt our historical trading signals and reverse-engineer our models—it would represent an existential threat to our edge. This isn’t hypothetical. It’s a risk we’re actively mitigating.
The Financial Sector’s Unique Vulnerability
Financial institutions are particularly exposed because they sit at the intersection of high-value data and long retention periods. Consider:
- Digital trust infrastructure: Banking systems, payment networks, and trading platforms all rely on public-key cryptography for authentication, digital signatures, and secure communications. A cryptographic foundation weakening could trigger fraud, identity theft, and systemic loss of trust.
- Regulatory compliance: Data protection regulations like GDPR and CCPA mandate adequate security. If quantum computers can break your encryption, you’re not just facing a technical problem—you’re facing regulatory penalties and legal liability.
- Operational technology: ATMs, point-of-sale terminals, and IoT devices often use lightweight encryption and have long replacement cycles. These systems can’t be easily updated, creating persistent vulnerabilities.
- Cross-border payments: SWIFT, real-time payment systems like FedNow and SEPA Instant, and cryptocurrency networks all depend on cryptographic security. A quantum attack on these systems could disrupt global financial flows.
The Citi Institute’s quantum threat report estimates that the probability of widespread breaking of public-key encryption is 19-34% by 2034, rising to 60-82% by 2044. Those aren’t comforting odds when you’re responsible for protecting trillions in assets.

Expert Analysis: The Race for Post-Quantum Cryptography
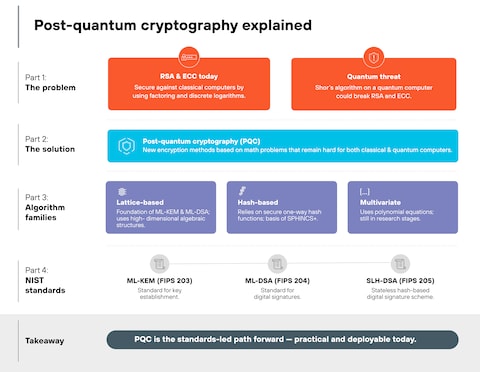
The good news—and yes, there is good news—is that the cryptographic community has been preparing for this moment. The National Institute of Standards and Technology (NIST) initiated its Post-Quantum Cryptography (PQC) standardization process in 2016, and the fourth and final PQC standard is expected by the end of 2024. These algorithms are designed to resist both classical and quantum attacks, using mathematical approaches fundamentally different from RSA and elliptic curve cryptography.
The challenge isn’t whether PQC algorithms exist—they do. The challenge is implementation at scale.
The Crypto-Agility Imperative
Crypto-agility—the ability to replace cryptographic methods without rebuilding entire systems—is the strategic capability that will separate winners from losers in the quantum era. Organizations that have built modular, abstracted cryptographic architectures can swap in PQC algorithms relatively quickly. Those that have hard-coded RSA into thousands of applications and systems face a multi-year, multi-billion-dollar migration.
At SavantTrade™, our trading infrastructure was designed with crypto-agility in mind. We use abstraction layers that separate cryptographic functions from application logic, standardized APIs for key management, and automated rotation protocols. When NIST finalizes its PQC standards, we’ll be able to implement them incrementally, starting with our highest-value data and most critical systems. This isn’t just good security practice—it’s a competitive advantage.
The Hybrid Approach
The most pragmatic near-term strategy is hybrid cryptography: combining classical algorithms (like RSA) with PQC algorithms. This provides protection against both current threats and future quantum attacks. If the PQC algorithm turns out to have an unexpected vulnerability, the classical algorithm provides a fallback. If a quantum computer emerges sooner than expected, the PQC algorithm provides protection.
IBM’s goal to achieve quantum advantage by the end of 2026 adds urgency to this timeline. If they succeed—and their roadmap suggests they might—then 2027 becomes the year when quantum computing transitions from “interesting research” to “clear and present danger.”
The Vendor Ecosystem Challenge
One of the biggest obstacles to PQC adoption is vendor readiness. Not all technology providers have clear PQC roadmaps. Some are waiting for NIST to finalize standards. Others are developing proprietary solutions. Many legacy systems simply can’t be updated.
Financial institutions need to be demanding PQC commitments from every vendor in their stack—especially for products with long replacement cycles like core banking systems, payment processors, and security infrastructure. Include PQC requirements in procurement processes. Establish SLAs for PQC support. Make it clear that quantum-safe capabilities are non-negotiable.
Real-World Implications: What Finance Must Do Now
The time for theoretical discussions is over. Financial institutions need to act, and they need to act now. Here’s a practical roadmap:
1. Conduct a Crypto Inventory and Risk Assessment
You can’t protect what you don’t know you have. Map every place RSA and public-key cryptography are used:
- Certificates and PKI infrastructure
- Identity and access management systems
- Software updates and code signing
- TLS/SSL connections
- Database encryption
- Email and messaging platforms
For each use case, assess the sensitivity of the data, the retention period, and the HNDL risk. Prioritize systems protecting data that needs long-term confidentiality.
2. Start Pilot Programs
Don’t wait for perfect standards. Begin small-scale PQC implementations now. Test performance and compatibility. Identify integration challenges early. Build internal expertise. The organizations that start experimenting today will be ready to scale when NIST finalizes its standards.
3. Implement Hybrid Cryptography
For new systems and major upgrades, deploy hybrid classical-PQC solutions. This provides immediate protection against HNDL attacks while maintaining compatibility with existing infrastructure.
4. Elevate to Board-Level Governance
Quantum risk isn’t an IT issue—it’s a strategic business risk. Boards need to understand the threat, the timeline, and the investment required. Establish quantum risk oversight committees. Integrate quantum preparedness into enterprise risk management. Allocate budget for multi-year migration programs.
The cost of PQC migration for large financial institutions could range from $50 million to $500 million or more over 5-10 years. That’s a significant investment, but it’s far less than the cost of a catastrophic quantum breach.
5. Engage with the Ecosystem
No institution can solve this alone. Join industry consortia. Participate in standards bodies. Share threat intelligence. Collaborate with quantum computing companies, PQC technology providers, and academic researchers. The financial sector needs to move together on this.
Future Outlook: Navigating the Quantum Transition
Let me be clear: I’m optimistic about our ability to navigate this transition. The cryptographic community has done remarkable work developing PQC algorithms. The technology exists. The standards are coming. The challenge is execution.
The most likely scenario is that Q-Day arrives sometime between 2030 and 2034, giving financial institutions a narrow but viable window to complete PQC migration. Some institutions will be well-prepared. Others will be scrambling. The difference will come down to decisions made in 2026 and 2027.
There’s also an opportunity here. The institutions that move first on quantum-safe infrastructure will gain competitive advantages:
- Customer trust: Market your quantum-safe capabilities. Attract security-conscious clients. Command premium pricing for quantum-protected services.
- Regulatory positioning: Be ahead of mandates rather than reacting to them. Influence standards rather than being subject to them.
- Innovation: Develop proprietary PQC solutions. Create quantum-safe financial products. Build quantum-resistant blockchain systems.
- Talent: Attract top cryptographers and quantum experts. Build internal capabilities that become strategic assets.
At Savanti Investments, we’re viewing the quantum transition as an opportunity to rebuild our security infrastructure from the ground up—not just to defend against quantum threats, but to create a more resilient, agile, and future-proof foundation for everything we do. Our Convirtio platform, which helps businesses navigate digital transformation, is being designed with quantum-safe principles from day one.
Conclusion: The Urgency of Now
The quantum encryption apocalypse isn’t coming in some distant, theoretical future. It’s approaching on a timeline measured in years, not decades. The breakthroughs of February and March 2026—Origin Pilot, the Pinnacle Architecture, the JVG Algorithm, Quantinuum’s hybrid milestone—are not isolated events. They’re inflection points in an accelerating curve.
Financial institutions have a choice. They can treat quantum risk as someone else’s problem, defer investment, and hope the timeline extends. Or they can act now—conduct crypto inventories, start pilot programs, implement hybrid solutions, elevate governance, and engage with the ecosystem.
The institutions that choose action will be the ones still standing when Q-Day arrives. The ones that choose delay will be explaining to regulators, customers, and shareholders why they weren’t prepared.
The clock is ticking. And it’s ticking faster than we thought.
Important Disclosures:
This article is provided for educational and informational purposes only and does not constitute investment advice, financial advice, trading advice, or any other sort of advice. The information presented reflects the personal views and opinions of the author and should not be construed as recommendations to purchase, sell, or hold any security or to engage in any investment strategy.
Savanti Investments, QuantAI™, SavantTrade™, and Convirtio are mentioned for illustrative purposes as examples of how organizations are approaching quantum risk. These references do not constitute endorsements or recommendations. Past performance is not indicative of future results.
Quantum computing and post-quantum cryptography are rapidly evolving fields. The timelines, probability estimates, and technical details presented in this article are based on publicly available information as of March 2026 and are subject to change. Readers should conduct their own research and consult with qualified cybersecurity professionals, legal advisors, and financial advisors before making decisions related to quantum risk mitigation.
This article may contain forward-looking statements regarding quantum computing capabilities, encryption vulnerabilities, and technology adoption timelines. Such statements are subject to risks, uncertainties, and assumptions. Actual results may differ materially from those expressed or implied.
No representation or warranty is made as to the accuracy, completeness, or reliability of any information contained herein. The author and Savanti Investments disclaim any liability for any direct, indirect, incidental, consequential, or special damages arising out of or in any way connected with the use of this article or the information contained herein.
Securities offered through registered broker-dealers in accordance with applicable securities laws. Savanti Investments and its affiliates are not registered investment advisors unless explicitly stated. This article does not constitute an offer to sell or a solicitation of an offer to buy any securities.
For more information about quantum risk management, post-quantum cryptography, and related topics, please consult with qualified professionals in cybersecurity, cryptography, and financial services.
© 2026 Braxton Tulin. All rights reserved.